안녕하세요.
오늘은 Cisco ASA VPN License를 설치 하는 방법에 대해서 알아보겠습니다.
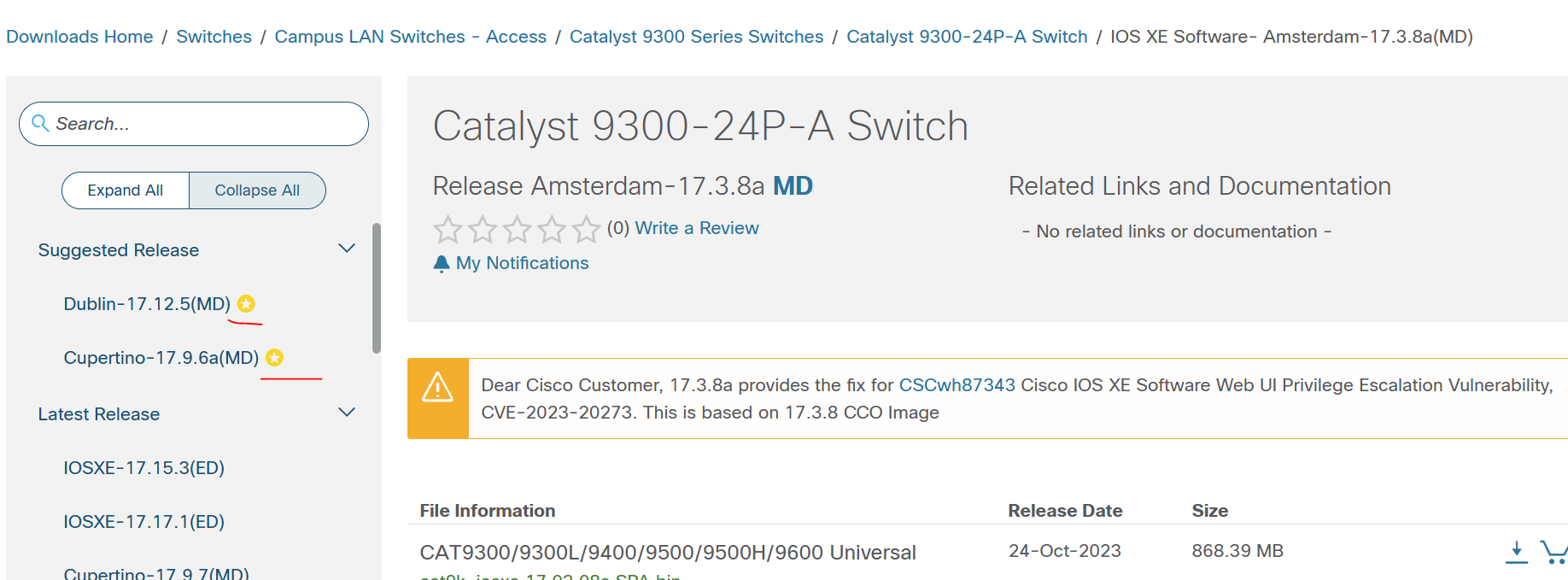
현재 Cisco Version는 아래와 같습니다.
asa# show version
Cisco Adaptive Security Appliance Software Version 9.20(3)20
SSP Operating System Version 2.14(2.121)
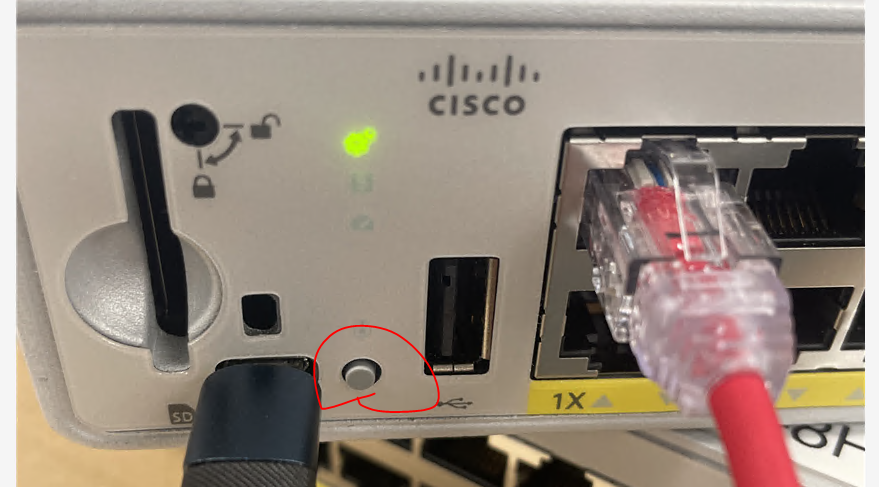
현재 고객사에서 cisco FPR3105를 ASA reimage해서 사용중에 있습니다.
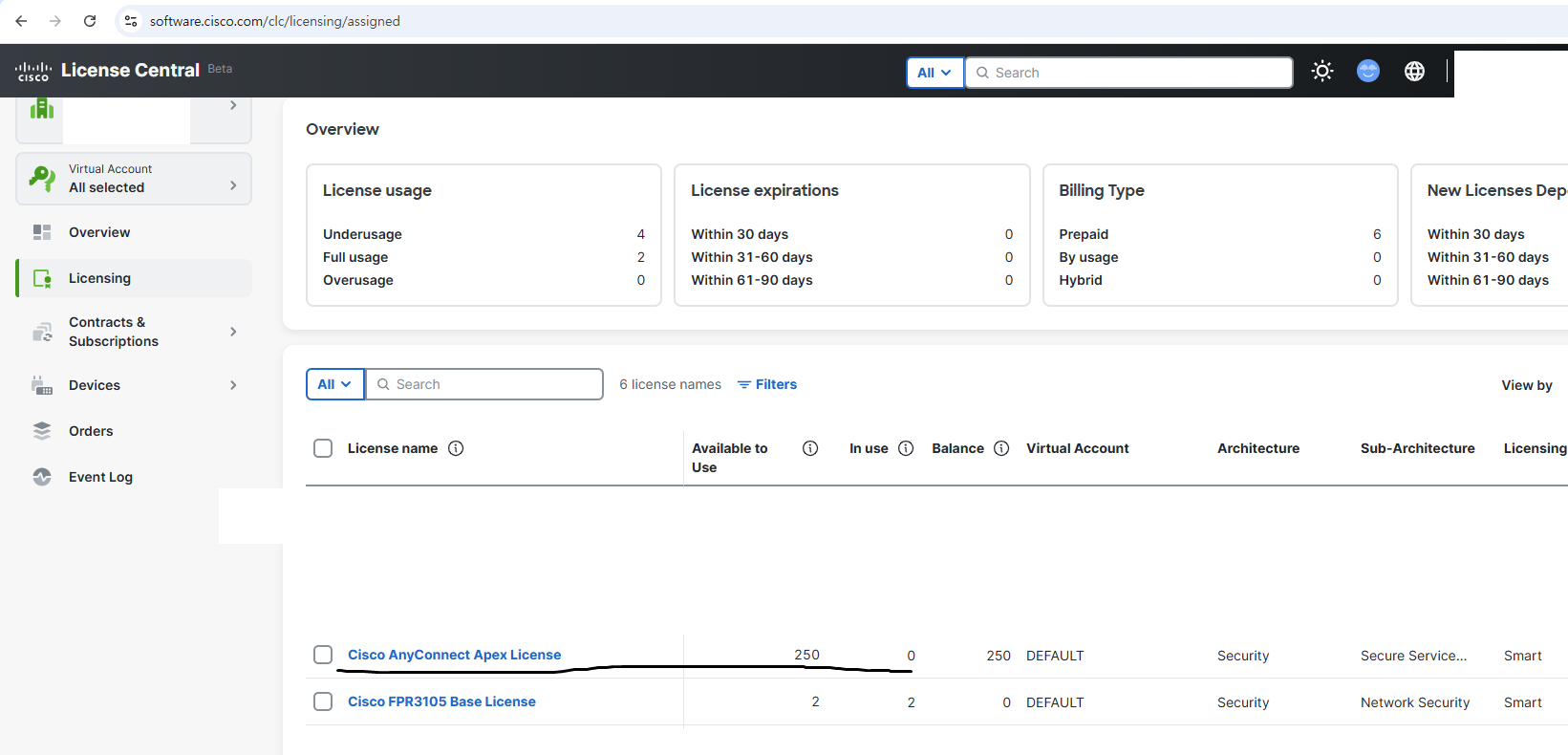
아래처럼 FPR3105 Base License는 전에 등록하였고, 이번에는 VPN License를 등록해보겠습니다.
Smart 라이센스에서 등록하는 방법은 똑같습니다.
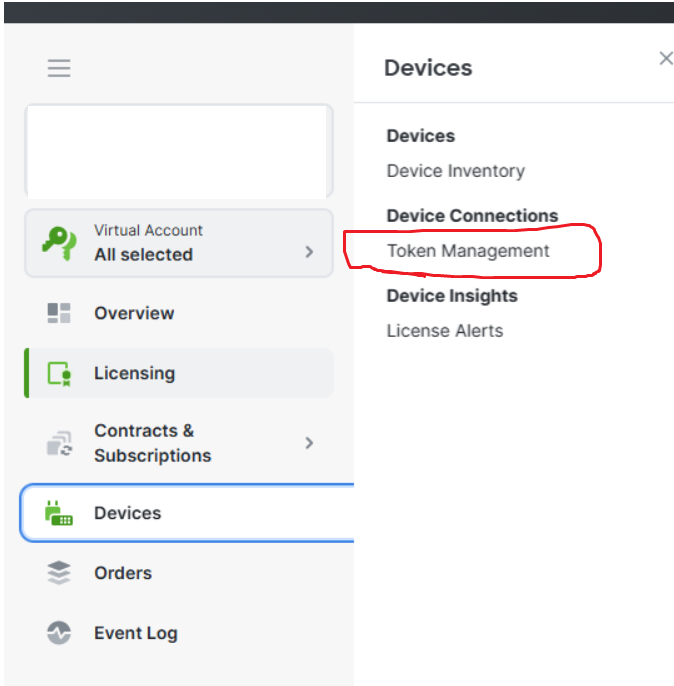
1. 토근을 생성하기위해서 아래처럼 Device -> Token Management를 클릭 합니다.
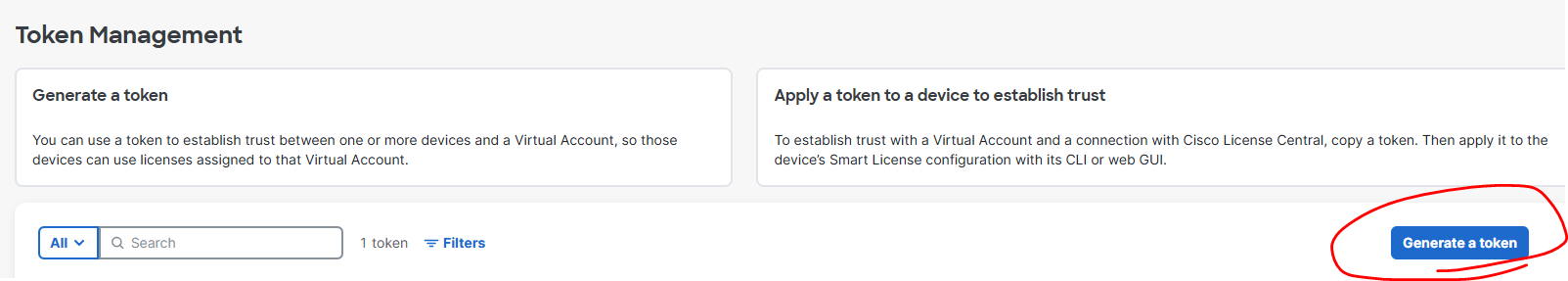
2. 아래처럼 Generate a token버튼을 클릭 합니다.
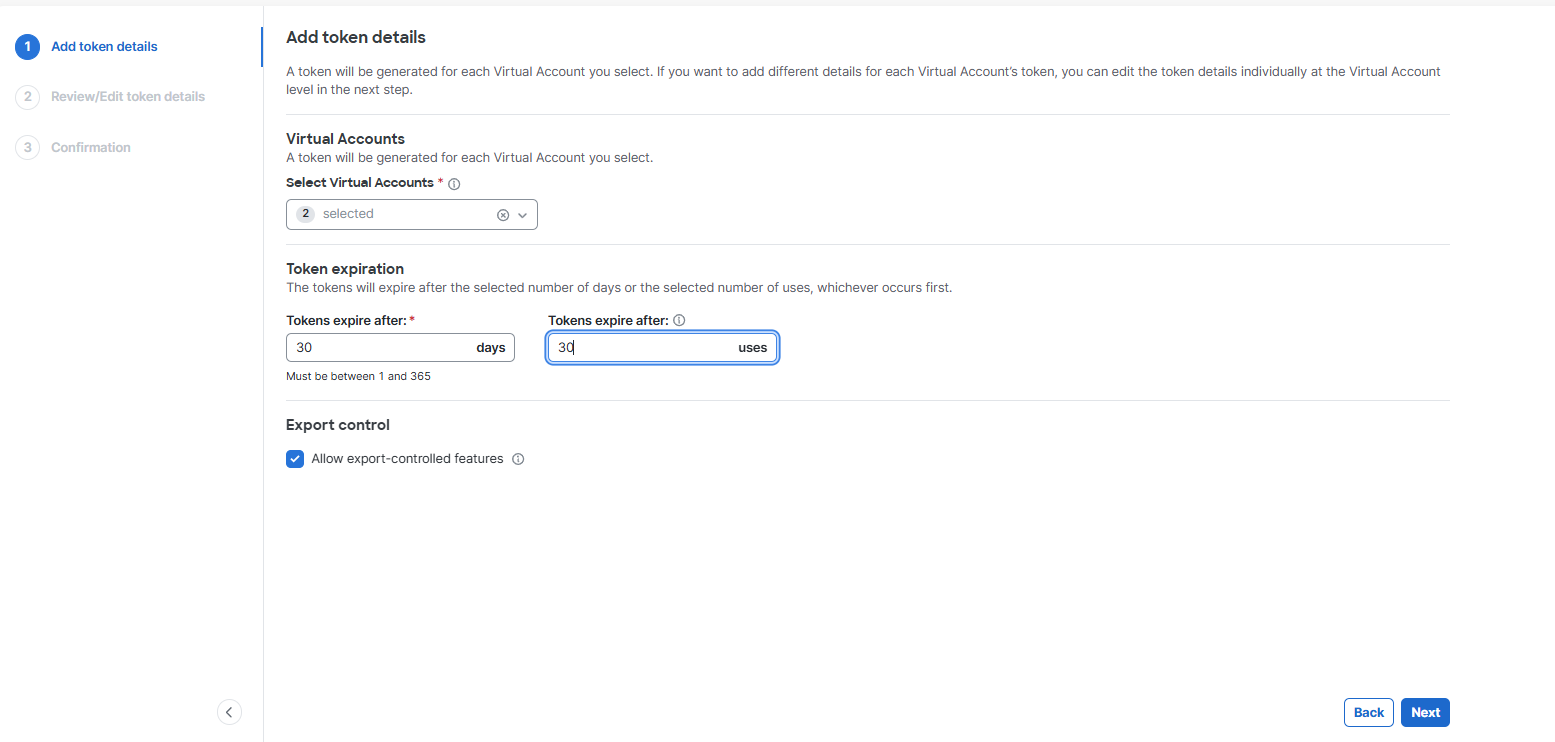
3. 아래처럼 입력하고 Next버튼을 클릭 합니다.
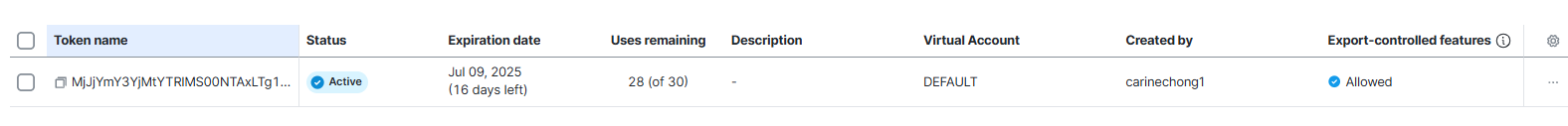
4. 아래처럼 토근이 생성 되었습니다.
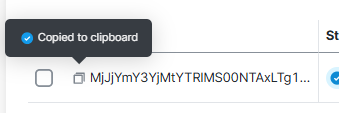
아래 Token name에 햄버거 버튼을 클릭해서 Token 값을 복사 합니다.
5. Cisco ASA를 콘솔또는 SSH 접속 합니다.
id_token에 위에 복사한값을 붙여넣기 하고 Enter를 클릭 합니다.
| license smart register idtoken id_token [force] |
6. 하지만 아무런 반응이 없습니다.
이유는 cisco ASA에서 dns를 설정해야지 domain으로 tools.cisco.com 또는 cisco license portal에 접속 가능 합니다
| asa/act/pri(config)# dns domain-lookup untrust asa/act/pri(config)# dns server-group DefaultDNS asa/act/pri(config-dns-server-group)# name-server 8.8.8.8 asa/act/pri(config-dns-server-group)# end asa/act/pri# ping google.com Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 142.251.12.100, timeout is 2 seconds: !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 1/6/10 ms asa/act/pri# asa/act/pri# asa/act/pri# ping tools.cisco.com Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 72.163.4.38, timeout is 2 seconds: !!!!! |
7. 똑같이 라이센스를 강제로 다시 한번 등록 합니다
| license smart register idtoken id_token [force] |
'CISCO > ASA 방화벽' 카테고리의 다른 글
| [ASA #11] - Godaddy SSL VPN for remote access VPN (0) | 2025.05.28 |
|---|---|
| [ASA #10] - Godaddy Domain for remote access VPN (0) | 2025.05.28 |
| [ASA #09] - Self-Signed Certificate for Remote Access VPN (0) | 2025.04.17 |
| [ASA #08] - SSL (0) | 2025.04.17 |
| [ASA #07] - NTP and NTP zone configuration (0) | 2025.04.15 |